Product
Take control of your software IP
Which Team? Which Devs? What Software?
Cloudsmith provides a flexible, powerful permissions system, putting you in complete control over who can access software. You can also integrate with your identity provider to control authentication, team membership and manage the lifecycle of your users.
- Role-based access control
- SSO via SAML group sync
- SCIM deprovisioning
- Team management
- Service bot accounts
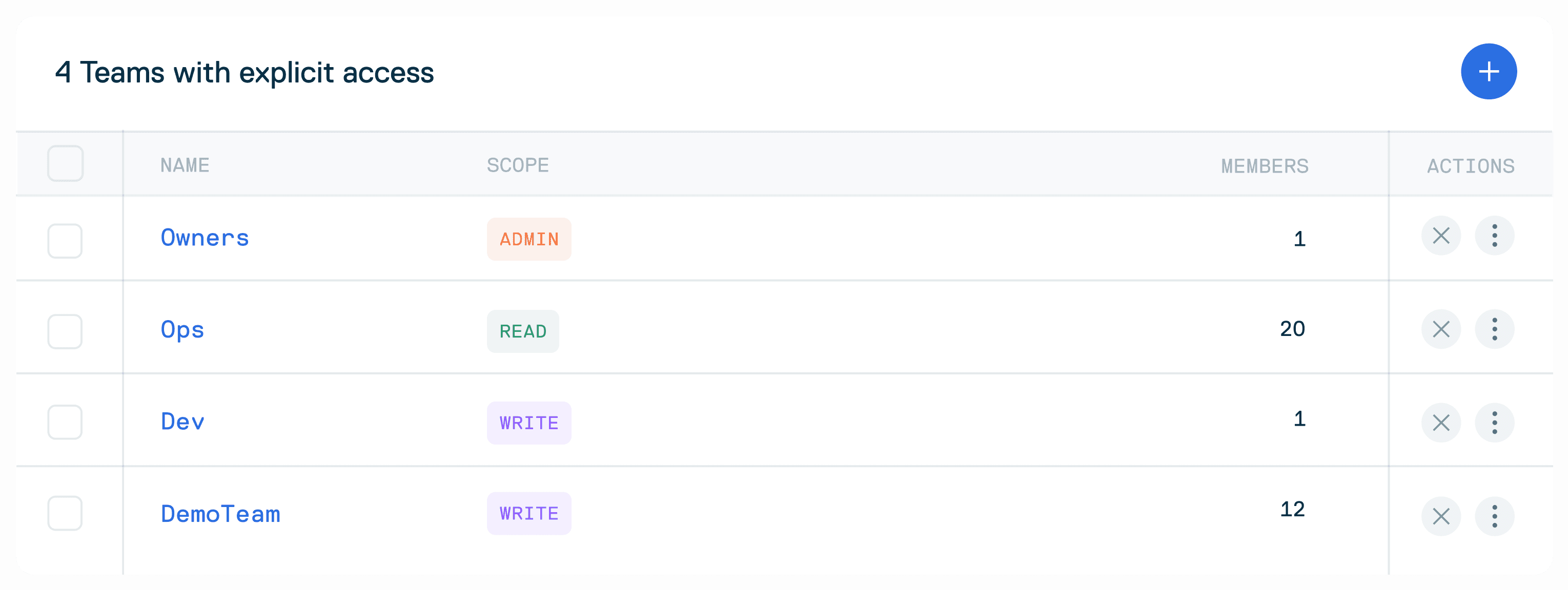
Fine grained access management
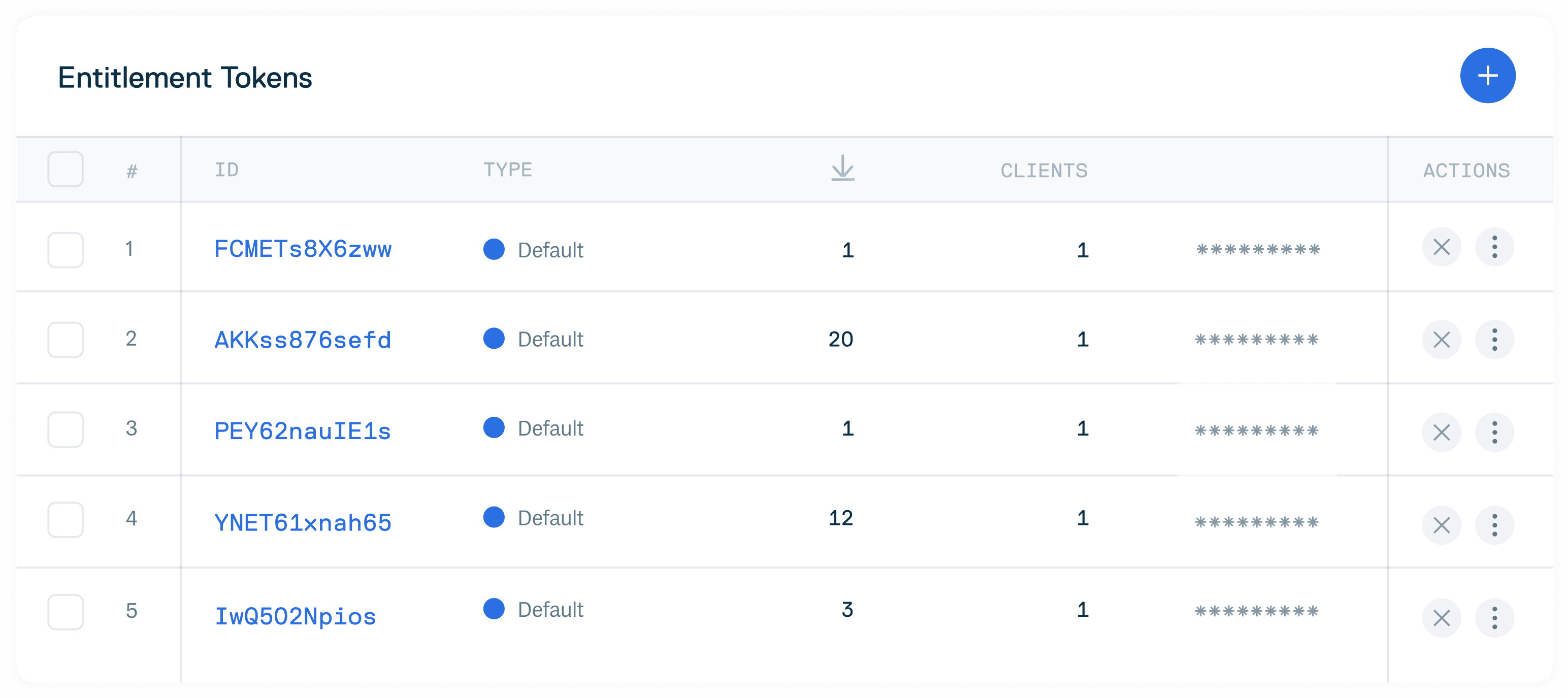
For customers who want to distribute software to customers, Cloudsmith’s entitlement tokens are the solution. With entitlement tokens, you can grant fine grained read-only access to your software, and control privileges at an individual package level.
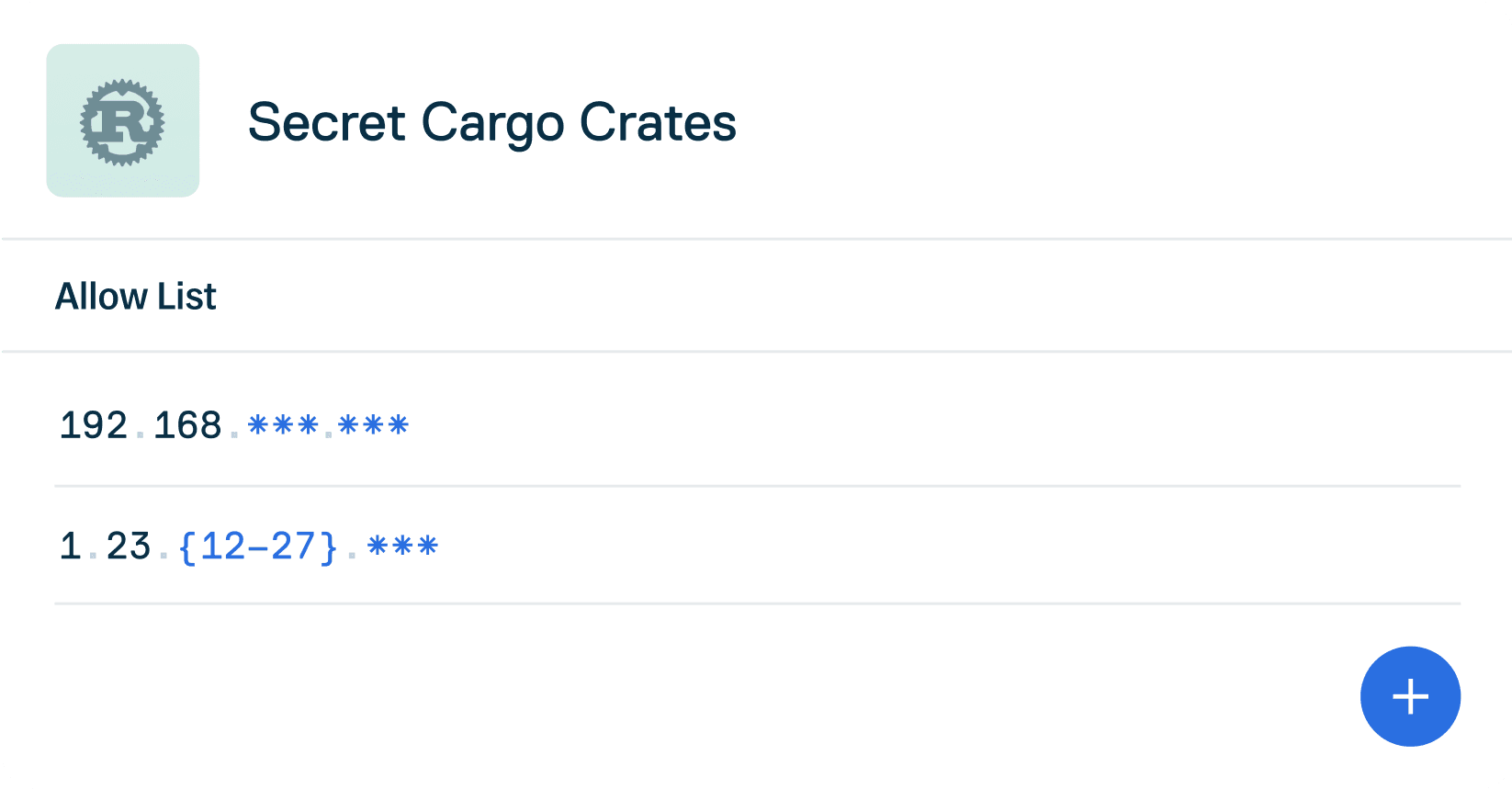
Global Control
If you need to add physical location security or compliance to your artifact management practices, you can do so with Geo/IP restrictions and custom storage regions.- GeoIP restriction
- Custom storage regions
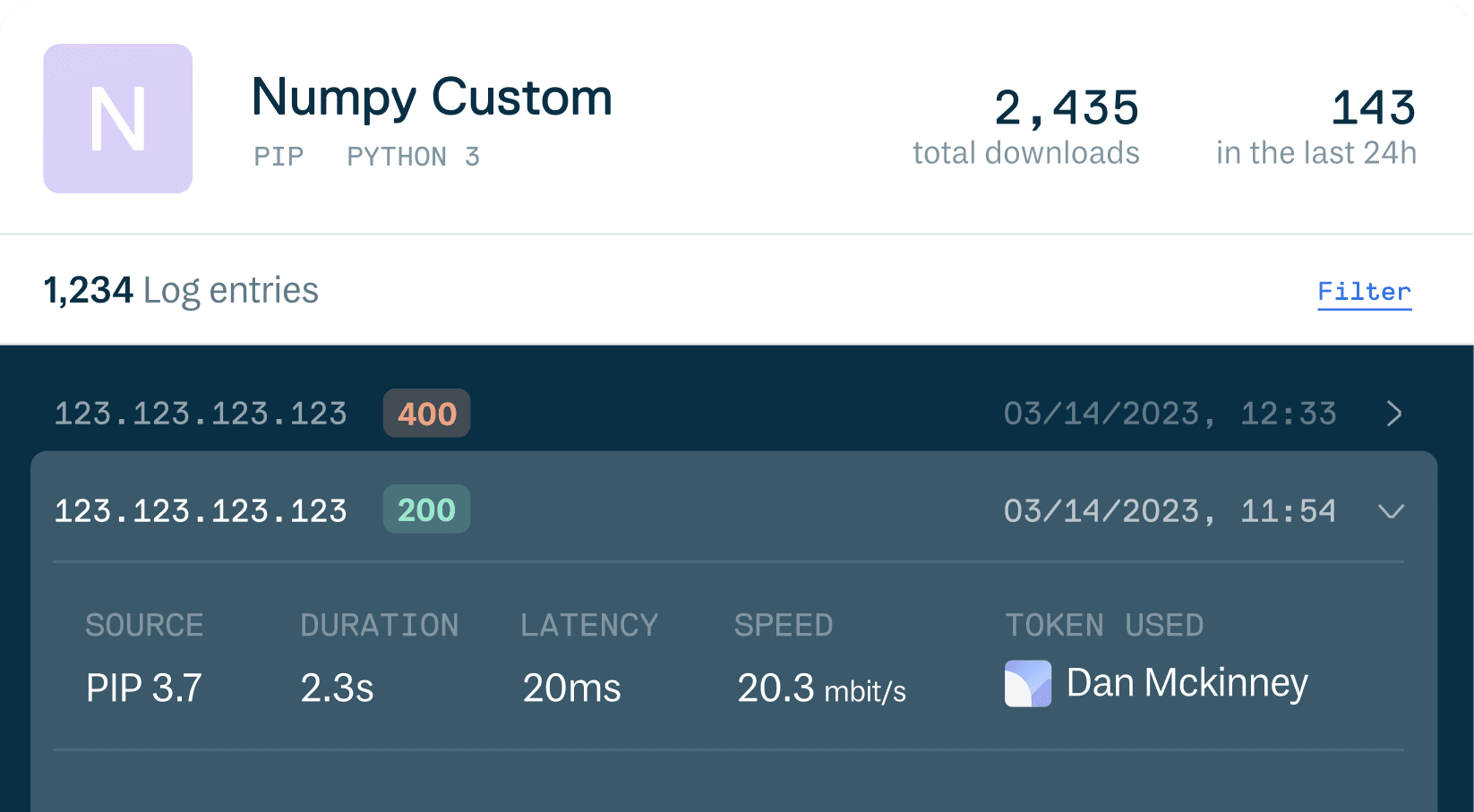
Track and Trace Usage
Get complete visibility and improved troubleshooting with Cloudsmith’s client logs, which track who is downloading your packages and where, and audit logs, which surface any changes made in the Cloudsmith platform and who made those changes.- Client log
- Audit Logs (+ API)
- Retention / lifecycle rules
CONTROL WHAT GETS SHIPPED
Ensure you only ship secure software to production with package promotion workflows.
Once you upload a binary, control when it moves from development to staging and to production, keeping the integrity of the asset, and a provenance trail, in place.
- Discuss your security must-haves
- Describe technical and team objectives
- Hear about best practices in software supply chain security
- Arrange an engineer-led demonstration